Newly shared CompTIA CS0-002 exam learning preparation program! Get the latest CS0-002 exam exercise questions and exam dumps pdf for free! 100% pass the exam to select
the full CompTIA CS0-002 dumps https://www.leads4pass.com/cs0-002.html the link to get VCE or PDF. All exam questions are updated!
leads4pass offers the latest CompTIA CS0-002 PDF Google Drive
[Latest updates] Free CompTIA CS0-002 dumps pdf download from Google Drive: https://drive.google.com/file/d/1uuA0o5lXyhqcgxZ6FBSG-TJcag_BDYX5/
Latest updated CompTIA CS0-002 exam questions and answers
QUESTION 1
A pharmaceutical company\\’s marketing team wants to send out notifications about new products to alert users of
recalls and newly discovered adverse drug reactions. The team plans to use the names and mailing addresses that
users have
provided.
Which of the following data privacy standards does this violate?
A. Purpose limitation
B. Sovereignty
C. Data minimization
D. Retention
Correct Answer: A
Reference: http://www.isitethical.eu/portfolio-item/purpose-limitation/
QUESTION 2
An organization suspects it has had a breach, and it is trying to determine the potential impact. The organization knows
the following:
The source of the breach is linked to an IP located in a foreign country. The breach is isolated to the research and
development servers. The hash values of the data before and after the breach are unchanged. The affected servers
were
regularly patched, and a recent scan showed no vulnerabilities.
Which of the following conclusions can be drawn with respect to the threat and impact? (Choose two.)
A. The confidentiality of the data is unaffected.
B. The threat is an APT.
C. The source IP of the threat has been spoofed.
D. The integrity of the data is unaffected.
E. The threat is an insider.
Correct Answer: BD
QUESTION 3
A security analyst has a sample of malicious software and needs to know what the sample does? The analyst runs the
sample in a carefully controlled and monitored virtual machine to observe the software behavior. Which of the following
malware analysis approaches is this?
A. White box testing
B. Fuzzing
C. Sandboxing
D. Static code analysis
Correct Answer: C
QUESTION 4
An analyst is searching a log for potential credit card leaks. The log stores all data encoded in hexadecimal. Which of
the following commands will allow the security analyst to confirm the incident?
A. cat log xxd -r -p | egrep \\’ [0-9] {16}
B. egrep \\'(3(0-9)) (16) \\’ log
C. cat log | xxd -r -p egrep \\'(0-9) (16)\\’
D. egrep \\’ (0-9) (16) \\’ log | xxdc
Correct Answer: C
QUESTION 5
The threat intelligence department recently learned of an advanced persistent threat that is leveraging a new strain of
malware, exploiting a system router. The company currently uses the same device mentioned in the threat report. Which
of the following configuration changes would BEST improve the organization\\’s security posture?
A. Implement an IPS rule that contains content for the malware variant and patch the routers to protect against the
vulnerability
B. Implement an IDS rule that contains the IP addresses from the advanced persistent threat and patch the routers to
protect against the vulnerability
C. Implement an IPS rule that contains the IP addresses from the advanced persistent threat and patch the routers to
protect against the vulnerability
D. Implement an IDS rule that contains content for the malware variant and patch the routers to protect against the
vulnerability
Correct Answer: A
QUESTION 6
A security analyst is reviewing the following log from an email security service.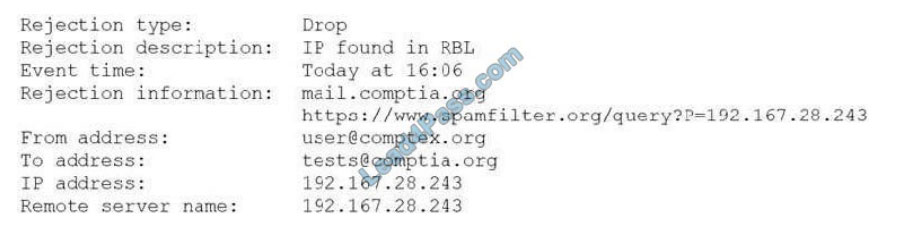
Which of the following BEST describes the reason why the email was blocked?
A. The To address is invalid.
B. The email originated from the www.spamfilter.org URL.
C. The IP address and the remote server name are the same.
D. The IP address was blacklisted.
E. The From address is invalid.
Correct Answer: D
Reference: https://www.webopedia.com/TERM/R/RBL.html
QUESTION 7
A small electronics company decides to use a contractor to assist with the development of a new FPGA- based device.
Several of the development phases will occur off-site at the contractor\\’s labs. Which of the following is the main
concern a security analyst should have with this arrangement?
A. Making multiple trips between development sites increases the chance of physical damage to the FPGAs.
B. Moving the FPGAs between development sites will lessen the time that is available for security testing.
C. Development phases occurring at multiple sites may produce change management issues.
D. FPGA applications are easily cloned, increasing the possibility of intellectual property theft.
Correct Answer: B
Reference: https://www.eetimes.com/how-to-protect-intellectual-property-in-fpgas-devices-part-1/#
QUESTION 8
A security analyst suspects a malware infection was caused by a user who downloaded malware after clicking
http:///a.php in a phishing email. To prevent other computers from being infected by the same malware variation, the
analyst should create a rule on the __________.
A. email server that automatically deletes attached executables.
B. IDS to match the malware sample.
C. proxy to block all connections to .
D. firewall to block connection attempts to dynamic DNS hosts.
Correct Answer: C
QUESTION 9
An analyst is reviewing a list of vulnerabilities, which were reported from a recent vulnerability scan of a Linux server.
Which of the following is MOST likely to be a false positive?
A. OpenSSH/OpenSSL Package Random Number Generator Weakness
B. Apache HTTP Server Byte Range DoS
C. GDI+ Remote Code Execution Vulnerability (MS08-052)
D. HTTP TRACE / TRACK Methods Allowed (002-1208)
E. SSL Certificate Expiry
Correct Answer: E
QUESTION 10
A security analyst received a series of antivirus alerts from a workstation segment, and users reported ransomware
messages. During lessons-learned activities, the analyst determines the antivirus was able to alert to abnormal behavior
but did not stop this newest variant of ransomware. Which of the following actions should be taken to BEST mitigate the
effects of this type of threat in the future?
A. Enabling sandboxing technology
B. Purchasing cyber insurance
C. Enabling application blacklisting
D. Installing a firewall between the workstations and Internet
Correct Answer: A
QUESTION 11
A cybersecurity analyst is dissecting an intrusion down to the specific techniques and wants to organize them in a
logical manner. Which of the following frameworks would BEST apply in this situation?
A. Pyramid of Pain
B. MITRE ATTandCK
C. Diamond Model of Intrusion Analysis
D. CVSS v3.0
Correct Answer: B
QUESTION 12
Joe, a penetration tester, used a professional directory to identify a network administrator and ID administrator for a
client\\’s company. Joe then emailed the network administrator, identifying himself as the ID administrator, and asked for
a current password as part of a security exercise. Which of the following techniques were used in this scenario?
A. Enumeration and OS fingerprinting
B. Email harvesting and host scanning
C. Social media profiling and phishing
D. Network and host scanning
Correct Answer: C
QUESTION 13
An organisation is assessing risks so it can prioritize its mitigation actions. Following are the risks and their probability
and impact:
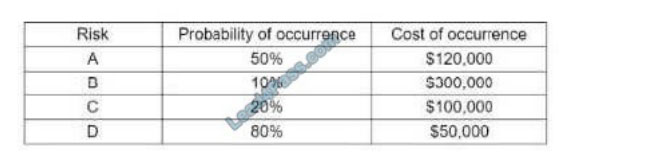
Which of the following is the order of priority for risk mitigation from highest to lowest?
A. A, B, C, D
B. A, D, B, C
C. B, C, A, D
D. C, B, D, A
E. D, A, C, B
Correct Answer: A
Summarize:
Examscode free to share CompTIA CS0-002 exam exercise questions, CS0-002 pdf! leads4pass updated exam questions and answers throughout the year!
Make sure you pass the exam successfully. Select lead4Pass CS0-002 Dumps to pass CompTIA CS0-002 exam “CompTIA Cybersecurity Analyst (CySA+)“.
ps.
Latest update leads4pass CS0-002 exam dumps: https://www.leads4pass.com/cs0-002.html (260 Q&As)
[Latest updates] Free CompTIA CS0-002 Dumps pdf download from Google Drive: https://drive.google.com/file/d/1uuA0o5lXyhqcgxZ6FBSG-TJcag_BDYX5/