A score of 750 or more on a scale of 100-900 will help you earn your CompTIA Security+ 2021 exam certification. Download the leads4pass SY0-601 dumps: https://www.leads4pass.com/sy0-601.html (PDF+ VCE). Helping you to easily exceed 750 points. leads4pass SY0-601 dumps include both PDF and VCE learning modes. You can choose whatever you want.
What is the CompTIA Security+ certification exam?
“CompTIA Security+ The knowledge and skills needed to assess the security posture of an enterprise environment and recommend and implement appropriate security solutions; monitor and secure hybrid environments, including cloud, mobile, and IoT; Understand applicable laws and policies, including governance, risk, and compliance principles; identity, analyze, and respond to security incidents and incidents.”
What are some popular ways to learn CompTIA Security+ SY0-601?
- Online training
- Free exam practice
- Exam Dumps
- Participate in community discussions
The above are some of the learning methods I have summarized, and I will tell you the advantages and disadvantages one by one:
First I declare that the analysis here comes from web data and my opinion and I only share individual standout sites.
Training:
[Udemy] The Most Popular Training Site
Pros: Video online training, one-on-one teacher training
Cons: long time, high cost of advanced training, tendency to solve problems with books
Free practice questions:
[Braindump4it], [Examscode] The most popular CompTIA free practice site
Pros: Free, updated throughout the year, the complete question bank
Cons: Only some free practice questions, no discussion
Exam dumps:
[leads4pass] Exam Dumps Top Sites
Pros: real questions, buy and use at any time, high pass rate, fast and convenient learning mode PDF + VCE
Cons: none
Community discussion:
[Quora], [Reddit] largest IT and wider discussion platform
Pros: Free, more people participating in discussions
Cons: long time, unable to acquire all knowledge
[2022.3 Update]Please take the 12-question SY0-601 free online test:
Note: Answers are posted at the bottom of the article
QUESTION 1:
Which of the following scenarios BEST describes a risk reduction technique?
A. A security control objective cannot be met through a technical change, so the company purchases insurance and is no longer concerned about losses from data breaches.
B. A security control objective cannot be met through a technical change, so the company implements a policy to train users on a more secure method of operation.
C. A security control objective cannot be met through a technical change, so the company changes as method of operation
D. A security control objective cannot be met through a technical change, so the Chief Information Officer (CIO) decides to sign off on the risk.
QUESTION 2:
Joe, an employee, is transferring departments and is providing copies of his files to a network share folder for his previous team to access. Joe is granting read-write-execute permissions to his manager but giving read-only access to the rest of the team. Which of the following access controls is Joe using?
A. FACL
B. DAC
C. ABAC
D. MAC
QUESTION 3:
A financial organization has adopted a new secure, encrypted document-sharing application to help with its customer loan process. Some important PII needs to be shared across this new platform, but it is getting blocked by the DLP systems. Which of the following actions will BEST allow the PII to be shared with the secure application without compromising the organization\\’s security posture?
A. Configure the DLP policies to allow all PII
B. Configure the firewall to allow all ports that are used by this application
C. Configure the antivirus software to allow the application
D. Configure the DLP policies to whitelist this application with the specific PII
E. Configure the application to encrypt the PII
QUESTION 4:
A network administrator is setting up wireless access points in all the conference rooms and wants to authenticate device using PKI. Which of the following should the administrator configure?
A. A captive portal
B. PSK
C. 802.1X
D. WPS
QUESTION 5:
A cloud administrator is configuring five compute instances under the same subnet in a VPC Three instances are required to communicate with one another, and the other two must he logically isolated from all other instances in the VPC. Which of the following must the administrator configure to meet this requirement?
A. One security group
B. Two security groups
C. Three security groups
D. Five security groups
QUESTION 6:
Which of the following would a European company interested in implementing a technical, hands-on set of security standards MOST likely choose?
A. GOPR
B. CIS controls
C. ISO 27001
D. ISO 37000
QUESTION 7:
Several employees return to work the day after attending an industry trade show. That same day, the security manager notices several malware alerts coming from each of the employee\\’s workstations. The security manager investigates but finds no signs of an attack on the perimeter firewall or the NIDS. Which of the following is MOST likely causing the malware alerts?
A. A worm that has propagated itself across the intranet, which was initiated by presentation media
B. A fileless virus that is contained on a vCard that is attempting to execute an attack
C. A Trojan that has passed through and executed malicious code on the hosts
D. A USB flash drive that is trying to run malicious code but is being blocked by the host firewall
QUESTION 8:
A security manager for a retailer needs to reduce the scope of a project to comply with PCI DSS. The PCI data is located in different offices than where credit cards are accepted. All the offices are connected via MPLS back to the primary datacenter. Which of the following should the security manager implement to achieve the objective?
A. Segmentation
B. Containment
C. Geofencing
D. Isolation
QUESTION 9:
A technician needs to prevent data loss in a laboratory. The laboratory is not connected to any external networks. Which of the following methods would BEST prevent the exfiltration of data? (Select TWO).
A. VPN
B. Drive encryption
C. Network firewall
D. File level encryption
E. USB blocker
F. MFA
QUESTION 10:
An organization relies on third-party video conferencing to conduct daily business. Recent security changes now require all remote workers to utilize a VPN to corporate resources. Which of the following would BEST maintain high-quality video conferencing while minimizing latency when connected to the VPN?
A. Using geographic diversity to have VPN terminators closer to end users
B. Utilizing split tunneling so only traffic for corporate resources is encrypted
C. Purchasing higher-bandwidth connections to meet the increased demand
D. Configuring QoS properly on the VPN accelerators
QUESTION 11:
A user is concerned that a web application will not be able to handle unexpected or random input without crashing. Which of the following BEST describes the type of testing the user should perform?
A. Code signing
B. Fuzzing
C. Manual code review
D. Dynamic code analysis
QUESTION 12:
While investigating a data leakage incident, a security analyst reviews access control to cloud-hosted data. The following information was presented in a security posture report.
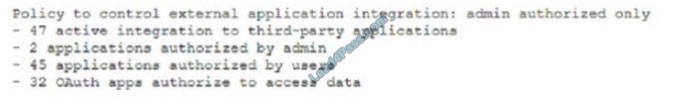
Based on the report, which of the following was the MOST likely attack vector used against the company?
A. Spyware
B. Logic bomb
C. Potentially unwanted programs
D. Supply chain
Verify the answer:
| Q1 | Q2 | Q3 | Q4 | Q5 | Q6 | Q7 | Q8 | Q9 | Q10 | Q11 | Q12 |
| B | D | D | C | B | A | A | A | BE | D | D | A |
PS. SY0-601 Free Exam Questions PDF Download-> https://drive.google.com/file/d/1GDKd3YfauPy_EKfCUgK7lLr0F2jthHiX/view?usp=sharing
Participating in the SY0-601 online practice test can test your current strength and help you improve your test experience. The free test has only 12 questions. The newly updated complete SY0-601 exam questions have 478 exam questions and answers. leads4pass SY0-601 Dumps: https://www.leads4pass.com/sy0-601.html Has complete exam questions with both PDF and VCE study modes to help you pass the exam easily.
![[2021] the latest update to Citrix 1Y0-440 dumps and free sharing of exam practice questions from Leads4Pass](https://www.examscode.com/wp-content/themes/blogstream/img/thumb-medium.png)